By Jane Melia
No matter what industry your clients are in, chances are they already have data stored in the cloud. A key concern for these companies, as well as for many more considering the move, is the exposure of that data to cyberattacks. When it comes to enterprise risk management, it’s best to anticipate the occurrence of a potential breach and act upon it rather than wonder whether it will happen or not. This article will lay out a few things you can think about to help mitigate the risks of storing and accessing sensitive data in the cloud.
While forecasts might differ, it is hard to deny that the demand for cloud services will continue to accelerate. This migration of IT services to the cloud is fueled by a host of drivers, from cost reduction and improving flexibility right through to disaster recovery and environmental impact. And of course, services such as Amazon Web Services and Microsoft Azure are making it much easier for organizations of all sizes to reap these benefits.
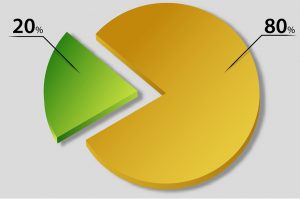
A recently published cloud security research study by digital security firm McAfee found that 80 percent of all IT budgets will be dedicated to cloud apps and solutions over the next year or so, but 49 percent of businesses noted they had to delay their cloud rollout due to a cybersecurity skills gap. While the cloud is increasingly considered a safer environment than most on-premises data centers, putting all the trust in your cloud service provider to take care of all aspects of security can be a risky move.
For one, there is a matter of who’s responsible—the client or the provider—when it comes to certain aspects of security in the cloud. Also, the regulatory landscape is changing; new regulations in New York state, for example, require banks and insurers to meet minimum cybersecurity standards and guidelines to report breaches. The question of control is also important: At the end of the day, you want to be confident that no one can access your sensitive data without your permission and knowledge.
With Breaches Inevitable, Encryption Is Key
Seamless encryption is recognized as the strongest protection against cyberattacks, and with good cause. If the data that is stolen is strongly encrypted, the breach may have little or no impact on your business—the attackers will effectively have nothing to show for their efforts. This is easier said than done, however, because there are many things to consider in order to pull this off well.
Authentication, policy controls, and strong key management are factors that need to be considered as part of a secure cloud implementation. For the highest security needs, you may wish to consider encrypting the data before it heads off to the cloud. Another very effective approach is to manage your own keys on your premises or in your data center, to ensure that the data encrypted in the cloud cannot be decrypted without your knowledge. Better still, double-wrapping of the encryption keys—with one set held by the cloud provider and the other by the customer—will allow full control and adds an extra layer of security against unauthorized access.
Key Management
Regardless of how strong the encryption itself is, it can be easily defeated without effective key management policies and systems in place. Some of the most complex and difficult parts of data encryption lie in generating, managing, and securing encryption keys in a varied IT landscape. A truly effective encryption solution will seamlessly integrate the very best key generation, key management, and cryptographic policy control with legacy systems and cloud service offerings.
There’s no shortcut: Effectively managing security risks requires implementing strong and operationally functional key and policy management. This means a solution that is:
- Highly secure and flexible enough to enable the policies that you need;
- Capable of generating high-quality keys that will not weaken the security of your encryption;
- Designed with operational readiness in mind;
- Scalable and centralized with simple usage and policy controls;
- Compliant with standards such as NIST ST 800-57 Part 1 and FIPS 140-2 Level 3 secure key storage and cryptographic operations; and
- Ideally located on your premises or in your carrier hotel to give you the control of your keys.
And it must, of course, accomplish all this while seamlessly integrating into your IT infrastructure.
In fact, the perceived challenges associated with this have made some CEOs and executive teams jokingly state that they may prefer the risk of a data breach over the almost-certain operational challenges of a poorly executed key management program. But this perspective is short-sighted. For one, the stakes are high, and with the inevitable migration to cloud-based IT solutions, risks are only increasing. In one of the most famous examples of the financial fallout from a data breach, retail giant Target is estimated to have lost over $250 million from direct and indirect damage related to its high-profile data breach in 2014. Furthermore, industry players are increasingly stepping up to the challenge, offering approaches that can meet the highest security needs with minimal operational headaches.
What the Future Holds
We are in a seemingly endless struggle between cybercriminals and companies seeking to defend their information and assets, with dramatic improvements in the tools becoming available to protect ourselves.
Take one example: encryption keys. Well-implemented encryption is extremely strong, to the point that cybercriminals can’t break the encryption—they have to find another way in. One of the ways that has been successfully used is to guess the keys. Indeed, most keys today are still generated using a pseudo-random number generator (PRNG). PRNGs are programs that start with a base number known as a seed that is generated from a random-ish physical component, such as the timing of the strokes on a user’s keyboard. The seed gets expanded using an algorithm, with the resulting key having limited “true” randomness. Both humans and computers are really bad at creating actual random strings, so if someone is able to measure the pattern of your keystrokes and/or guess or break one of the algorithms used, they can reverse-engineer the other inputs and predict the next numbers in the “random” sequence. Find the pattern, break the code, and the jackpot (or your encrypted data) is theirs.
Until recently, users have had to make a trade-off between quality and quantity when it comes to randomly generated strings. Faced with this issue, companies have figured out how to use the inherently random properties of the quantum world to generate true random numbers. With truly random keys, there are no patterns to be discovered as with pseudo-random numbers, making the keys fully resistant to even the most powerful computer available today.
In parallel, dramatic progress is being made in key and policy management features and in the development of on-premise solutions that can seamlessly work with the cloud. Generating and managing your own keys of the highest quality while still being able to reap the benefits of the cloud is now an attainable goal.
When considering how the threat landscape is already evolving, you must assume that data that won’t be safe tomorrow is, in fact, not safe today. With the complexities and points of friction added by the inevitable cloud-based migration of IT systems, there is a heightened possibility of risk for breaches, theft, regulatory non-compliance, and the accumulated negative impact of public awareness about a breach of the sort Target suffered.
While the challenges facing clients are great, they are not insurmountable. The technology to overcome those challenges does exist, so the risk inherent to inevitable trends in cloud usage can be managed—but not with the systems and technologies that worked on yesterday’s problems.
JANE MELIA is vice president of strategic development at QuintessenceLabs.